Endpoint Detection and Response (EDR)

Executive Summary
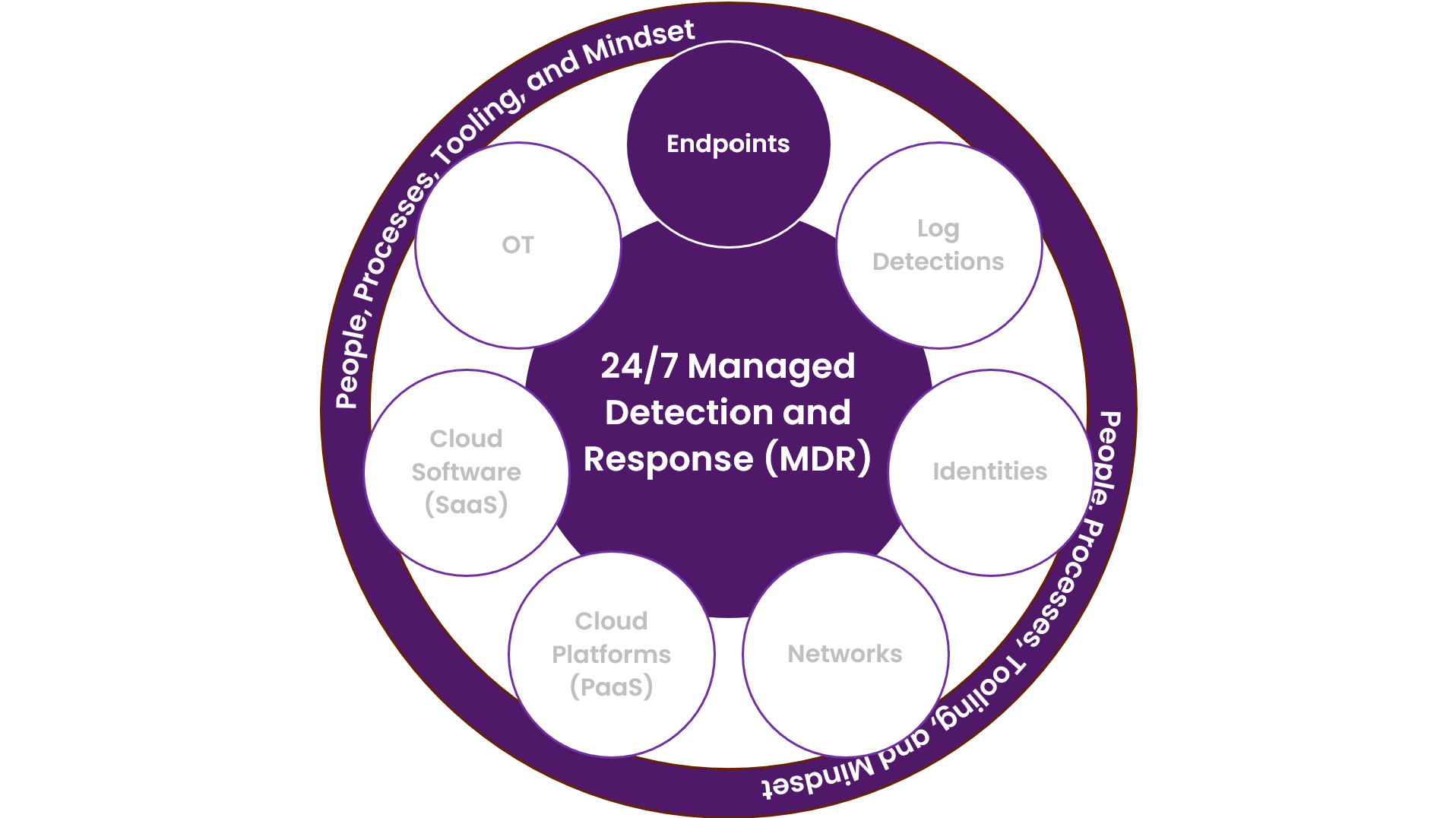
Endpoint detection and response (EDR) is a security solution that continuously monitors end-user devices (like workstations, laptops, and mobile phones) and servers to detect and respond to cyber threats. An EDR works great together with an NDR solution.
Here’s how it works:
- Monitoring: EDR solutions record the activities and events taking place on endpoints, providing security teams with the visibility they need to uncover incidents.
- Detection: EDR uses various data analytics techniques to detect suspicious system behavior. It can recognize threats and determine what kind of threat it is.
- Response: Once a threat is detected, EDR provides remediation suggestions to handle the affected systems. It can contain the threat, keep it from spreading, and roll back the damage it caused.
- Threat Hunting: EDR allows for proactive defense. Threat hunters work to hunt, investigate, and advise on threat activity in the environment.
In essence, EDR is like a security guard who never sleeps. It constantly watches over your digital devices, ready to detect and respond to any potential threats. It’s a crucial part of modern cybersecurity strategies, helping to protect your organization’s information and systems from cyber threats.
My Antivirus Is Modern and Up to Date; Isn’t That Enough?
Traditional antivirus solutions focus on file-based threats and signatures. EDR solutions are more comprehensive and focus on endpoint behavior to find threats and malicious activities.
Endpoint Detection and Response
Monitoring
The EDR agent constantly monitors the endpoint and reports when patterns in the system or end-user behavior appear to be malicious. Combined with an anti-malware engine, it monitors by scanning files and memory on the endpoint and reports to a backend system when an alert occurs. There are both on-premise and cloud-based EDR solutions on the market today, so depending on the setup your company requires, there is a product that fits your needs.
Detection
What sets the EDR aside from a traditional antivirus is its possibility to detect threats using sophisticated algorithms, machine learning and combining it with threat intelligence feeds. The detection engine can discover irregular and unusual endpoint behavior even though the files that are accessed and used are not malicious. When malicious activities are identified, it will send a detection alert so a threat analyst can investigate it and take responsive actions.
Response
One of the most important features of an EDR agent is its response capabilities. These allow a threat analyst to isolate or quarantine an endpoint to stop an infection or attack from spreading further. Isolation is a virtual way of disconnecting the network cable or blocking Wi-Fi access while still retaining access from the monitoring backend system to the endpoint in question.
Threat Hunting
Threat hunting is an iterative process to proactively search for and identify weaknesses in the system or endpoint behavior. The approach combines digital forensics with incident response tactics to identify possible entry points for an attacker or uncover previously unknown cyber threats inside the organization. Threat hunters assume that the threat actor is already inside, and they focus on finding unusual behavior prior to malicious activities. The primary goal for a threat hunter is to identify a possible attack vector and mitigate it before the attacker discovers it.
FAQ
EDR stands for endpoint detection and response. It’s a cybersecurity technology that continuously monitors and responds to threats on endpoints, such as laptops, workstations, servers, and mobile phones.
EDR is important because it provides real-time threat detection, allowing for quick response and mitigation of cyber threats.
Unlike traditional antivirus, which relies on known signatures, EDR monitors endpoint behavior to detect anomalies and potential threats.
Good EDR solutions should include features like real-time monitoring, threat detection, incident response capabilities, and integration with threat intelligence feeds.
EDR implementation can be challenging due to factors like system compatibility issues, the need for skilled personnel, and potential privacy concerns.