
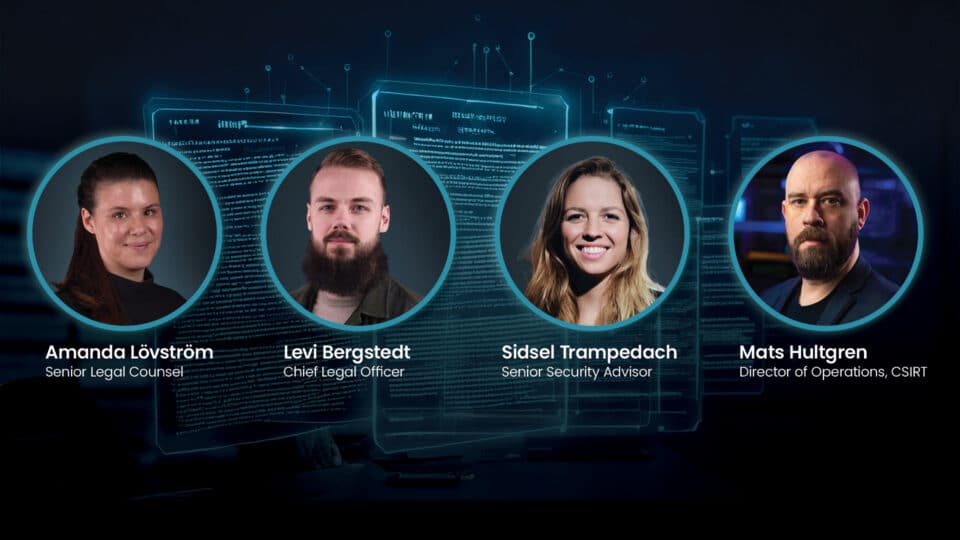
Tackling Human Insider Risk: From detection to action with Truesec MDR
| 09:00-09.30 (CEST)
-

Cybersecurity webinars
Join the latest cybersecurity webinars for tech professionals and business leaders, all brought to you by leading experts.

| 09:00-09.30 (CEST)


| 9.00-9.30 (CEST)



| 09:00



| 09.00-09.45




Webinar




Webinar


Webinar



Webinar




Webinar




Webinar



Webinar


Webinar



Webinar


